ShellTorch: Multiple Critical Vulnerabilities in PyTorch Model Server (TorchServe) (CVSS 9.9, CVSS 9.8) Threatens Countless AI Users
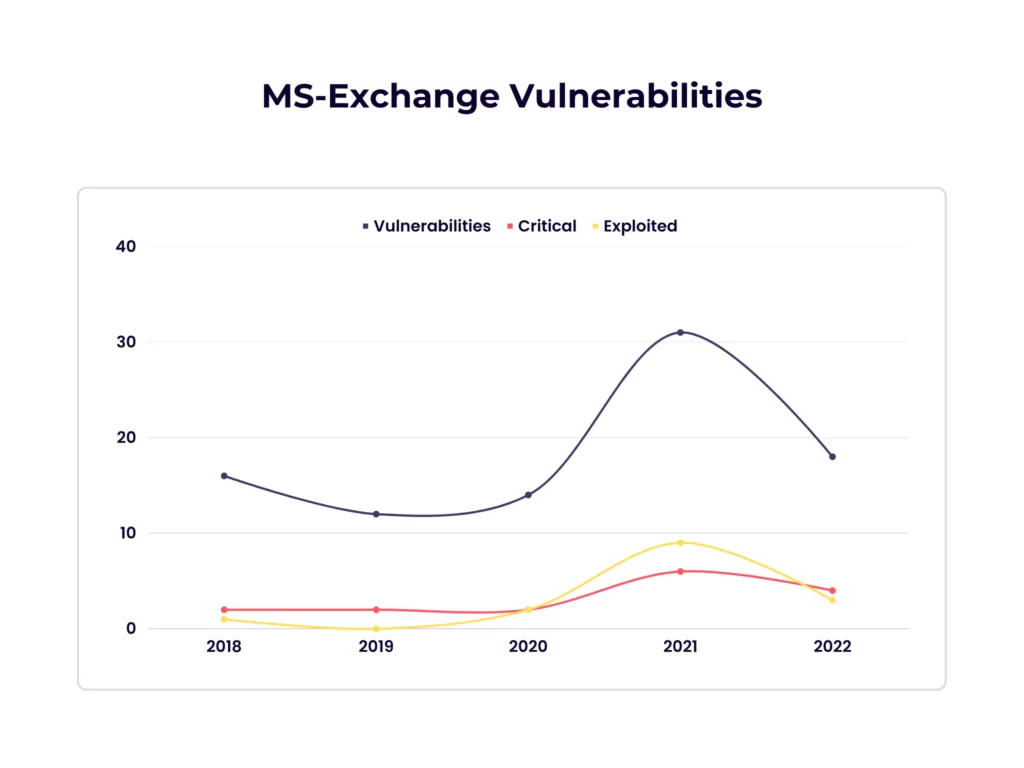
Threat Assessment: Active Exploitation of Four Zero-Day Vulnerabilities in Microsoft Exchange Server
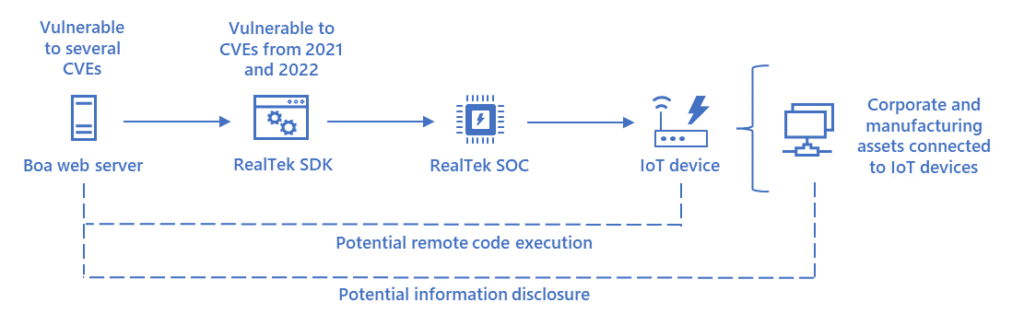
Vulnerable SDK components lead to supply chain risks in IoT and OT environments | Microsoft Security Blog
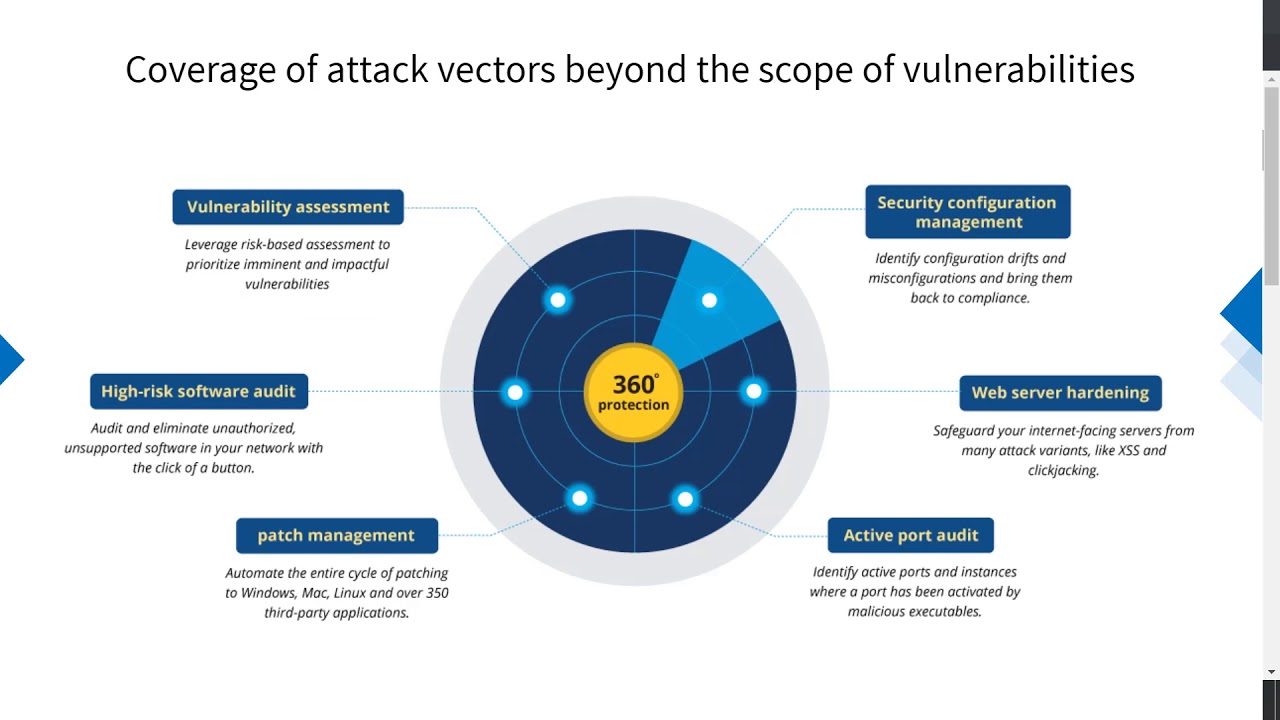
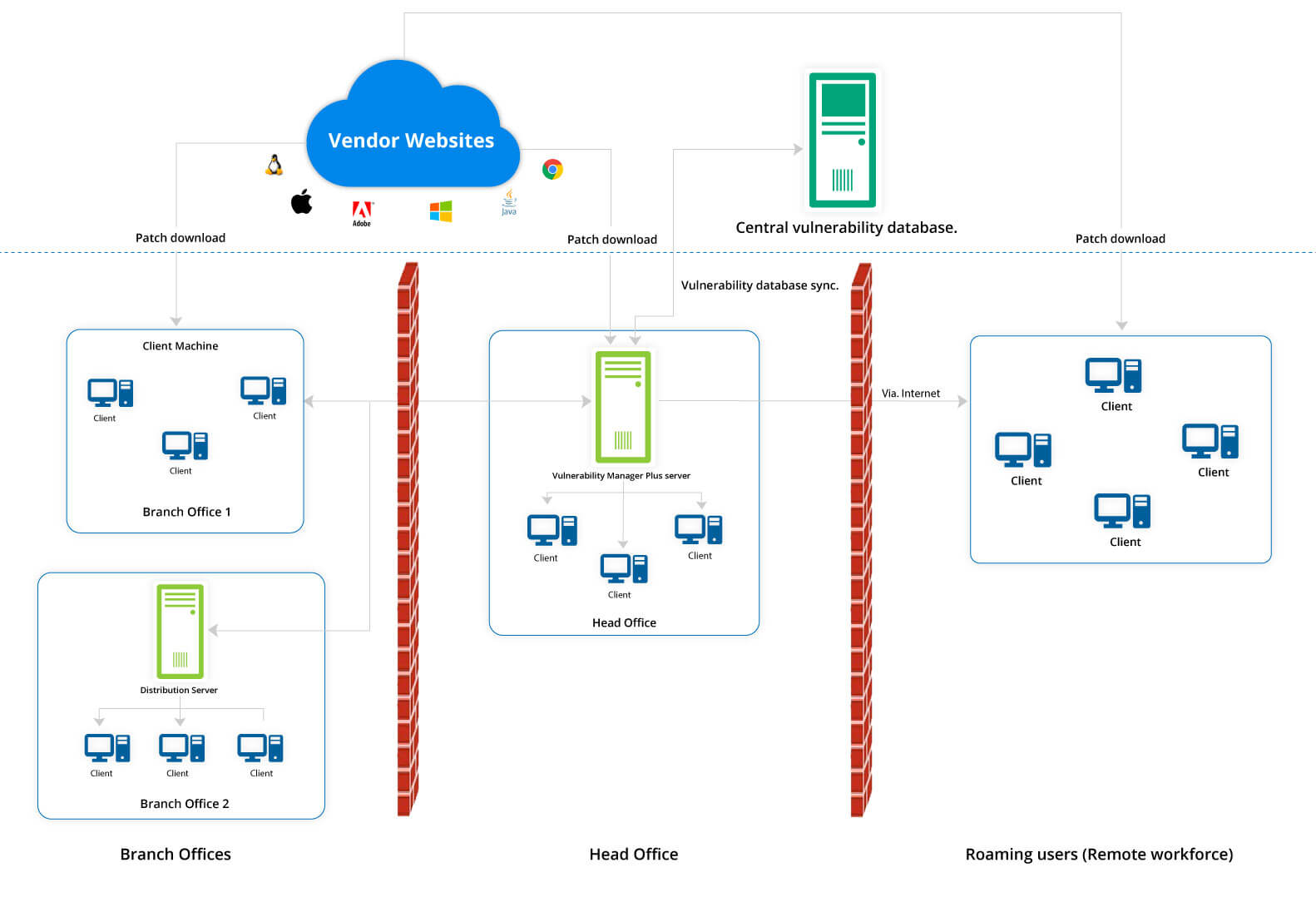
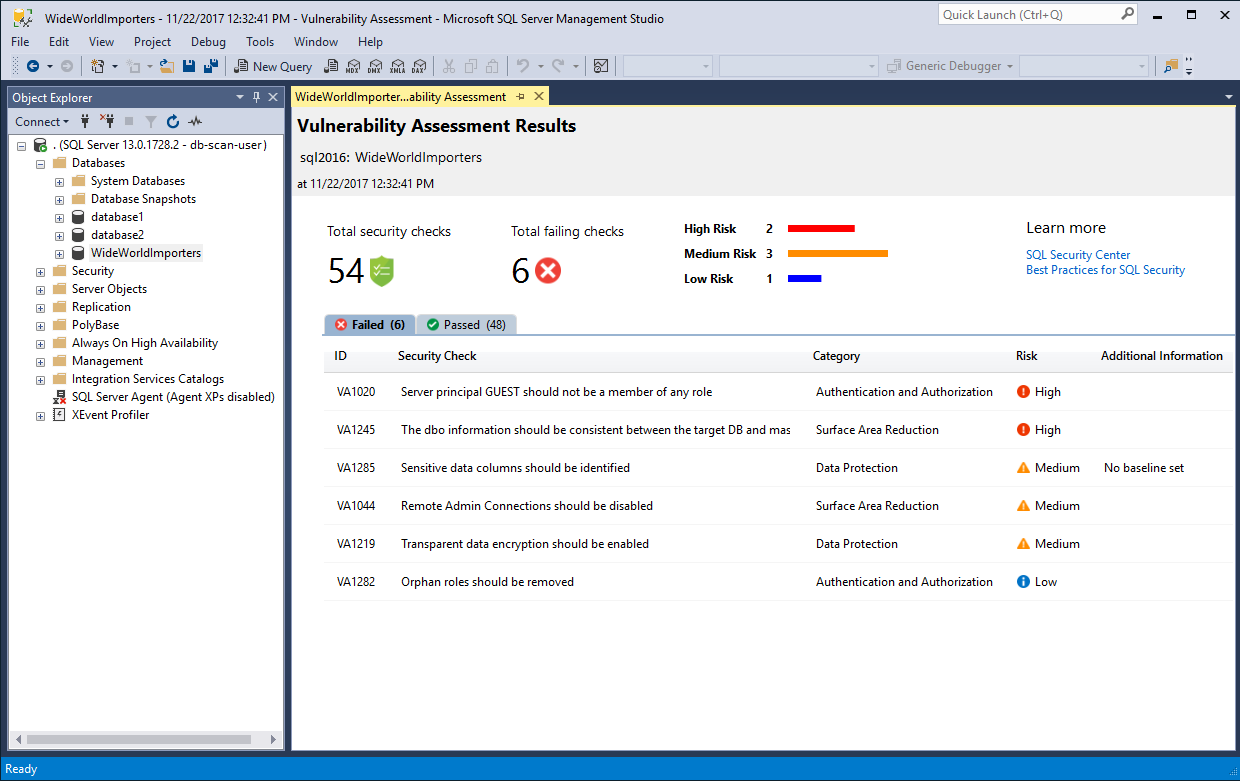
What is vulnerability management? | Vulnerability management process - ManageEngine Vulnerability Manager Plus
What is vulnerability management? | Vulnerability management process - ManageEngine Vulnerability Manager Plus
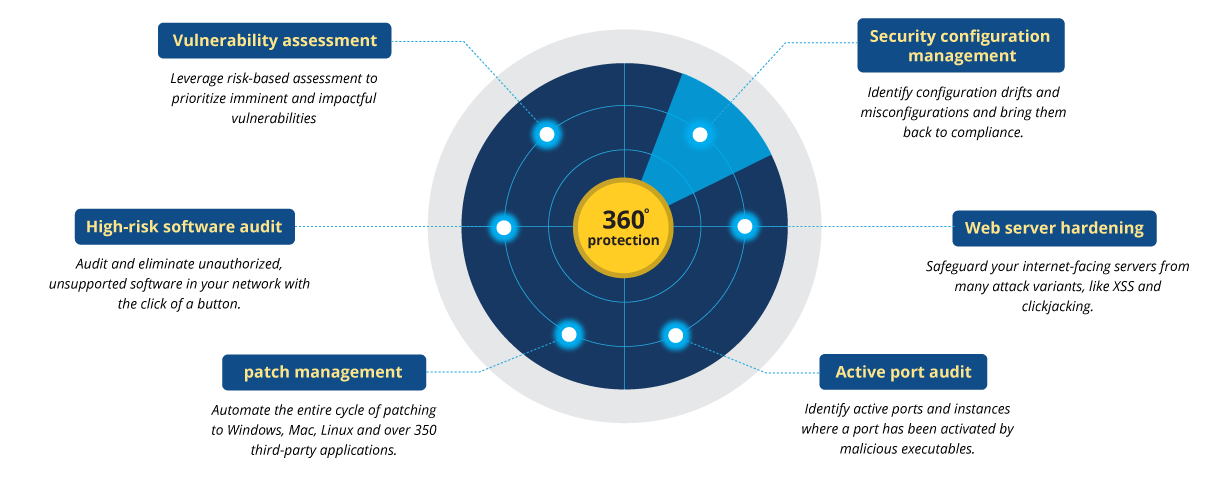
What is vulnerability management? | Vulnerability management process - ManageEngine Vulnerability Manager Plus

Critical Vulnerabilities in Atlassian Confluence: Zero-Day Exploits targeting CVE-2023-21715, Application Security, and Nation-State Threats - Phoenix Security