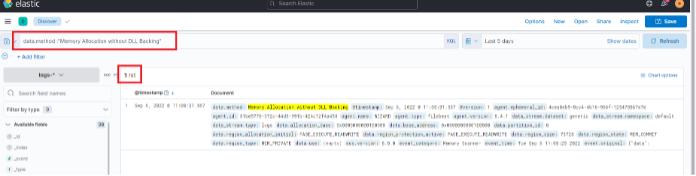
GuidedHacking on X: "🕵️Detecting Sus Threads with Memory Checks 💡 Strategies for Evading Thread Detection ➡️https://t.co/3yK8DKczlr https://t.co/PA7ooVvPPE" / X
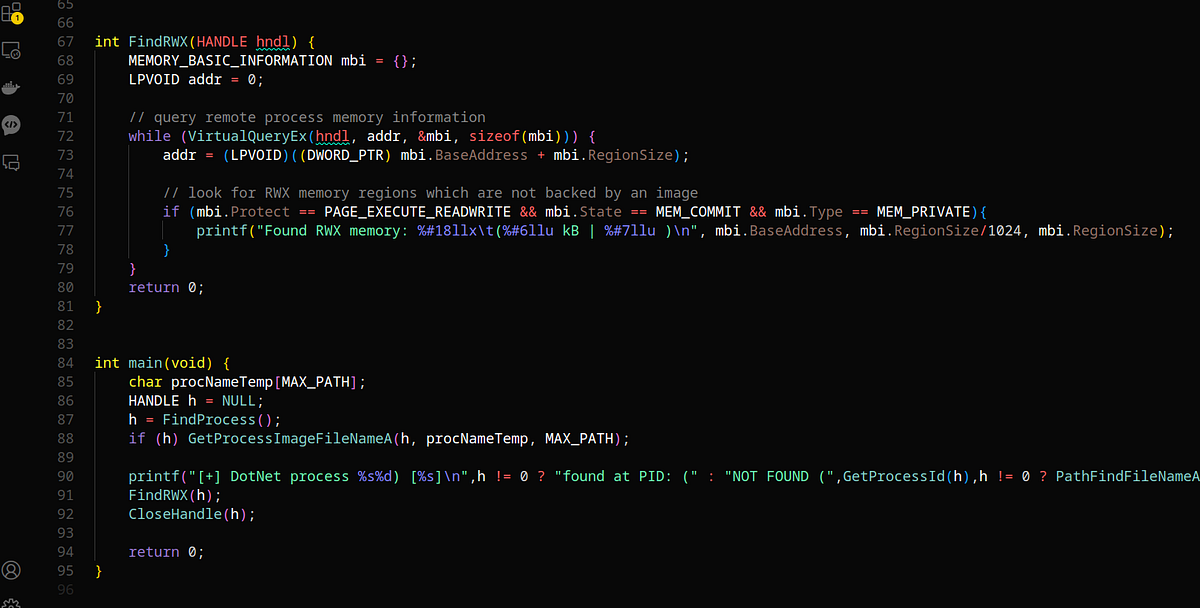
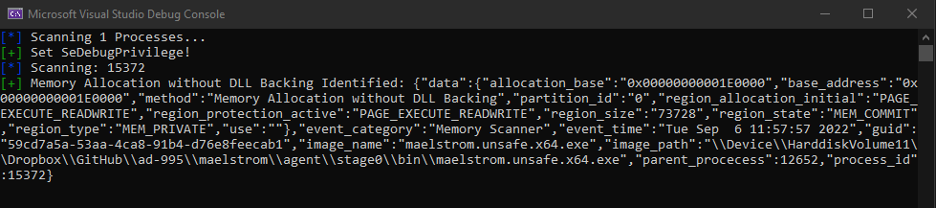
Beware of Unknown Areas to Notify Adversaries: Detecting Dynamic Binary Instrumentation Runtimes with Low-Level Memory Scanning | SpringerLink
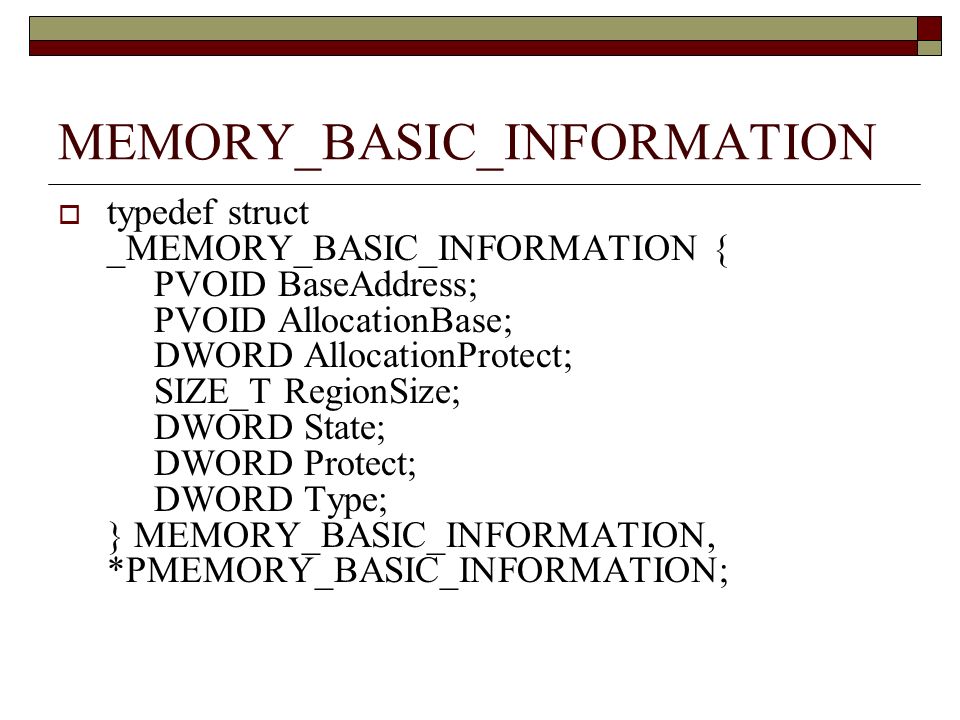
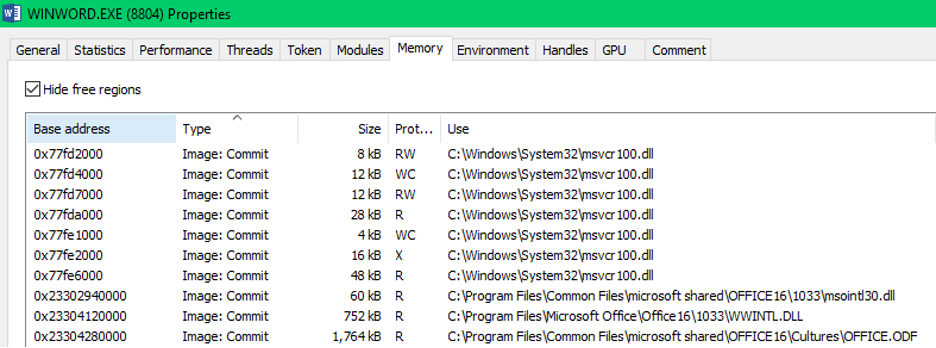
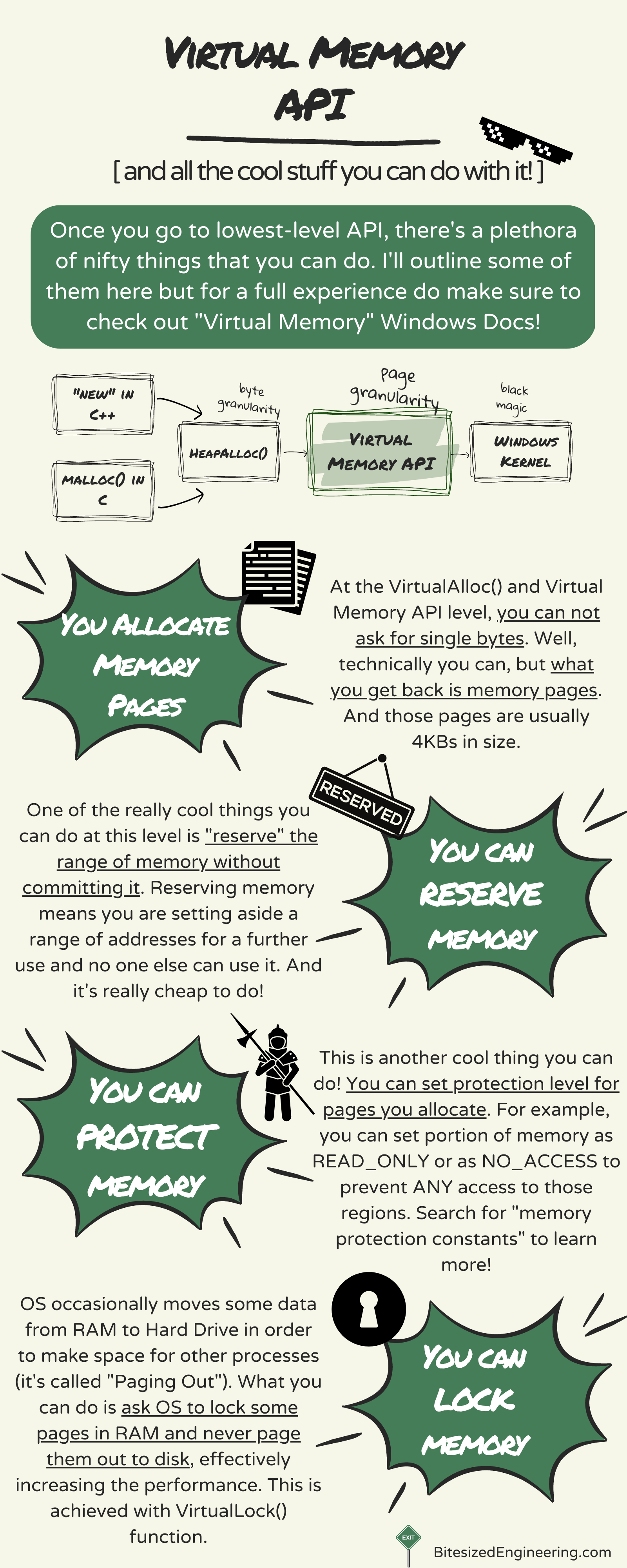
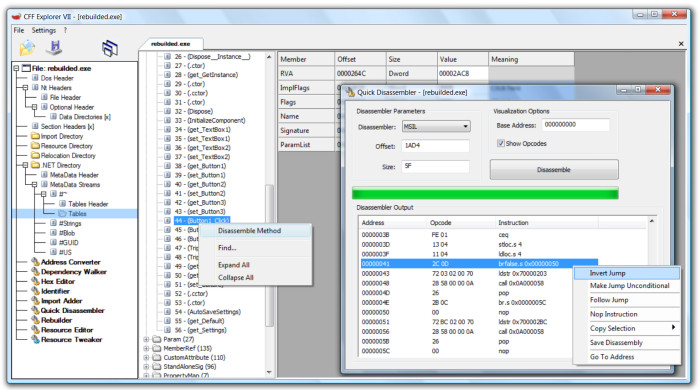
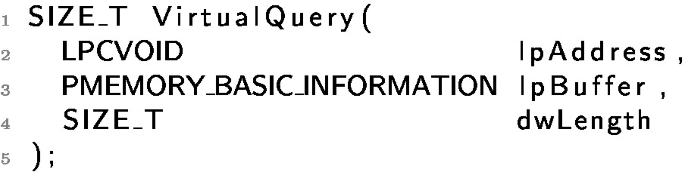
Win32 Programming Lesson 15: Practical Windows Memory (If you can read this you have good vision) - ppt download
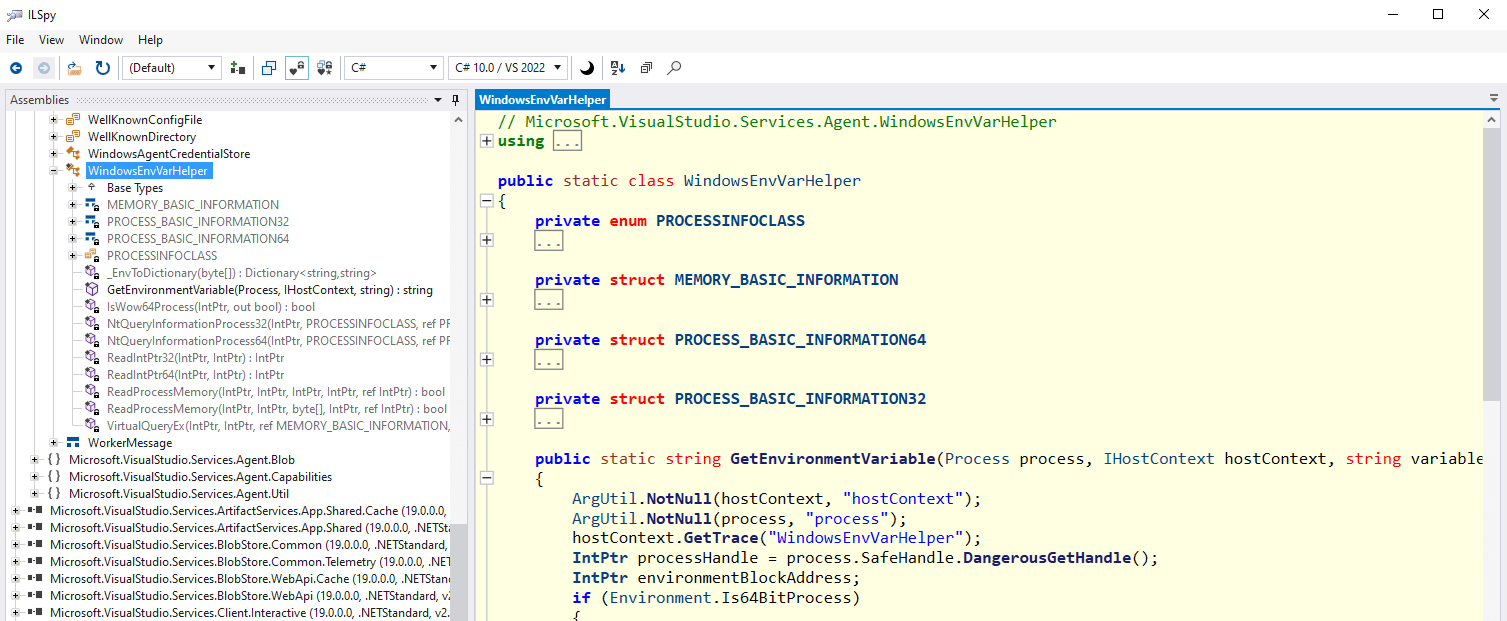
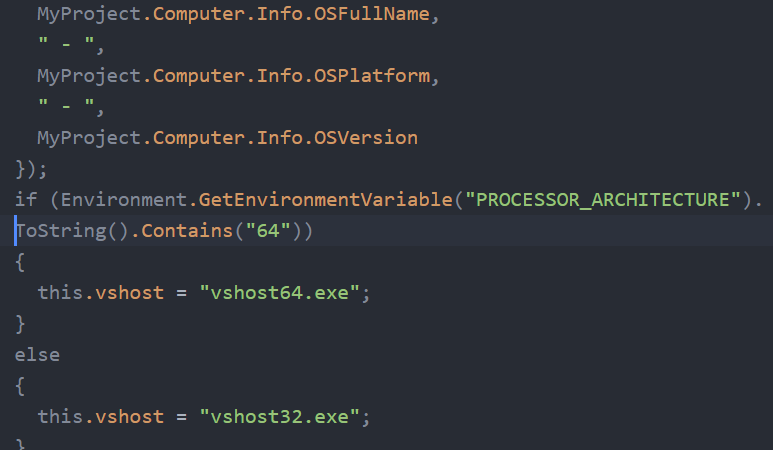
Azure DevOps CICD Pipelines - Command Injection with Parameters, Variables and a discussion on Runner hijacking