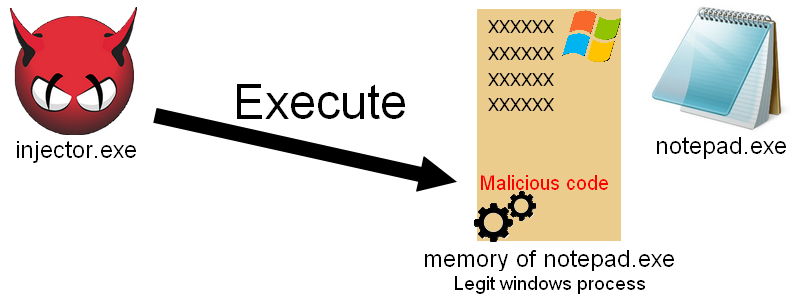
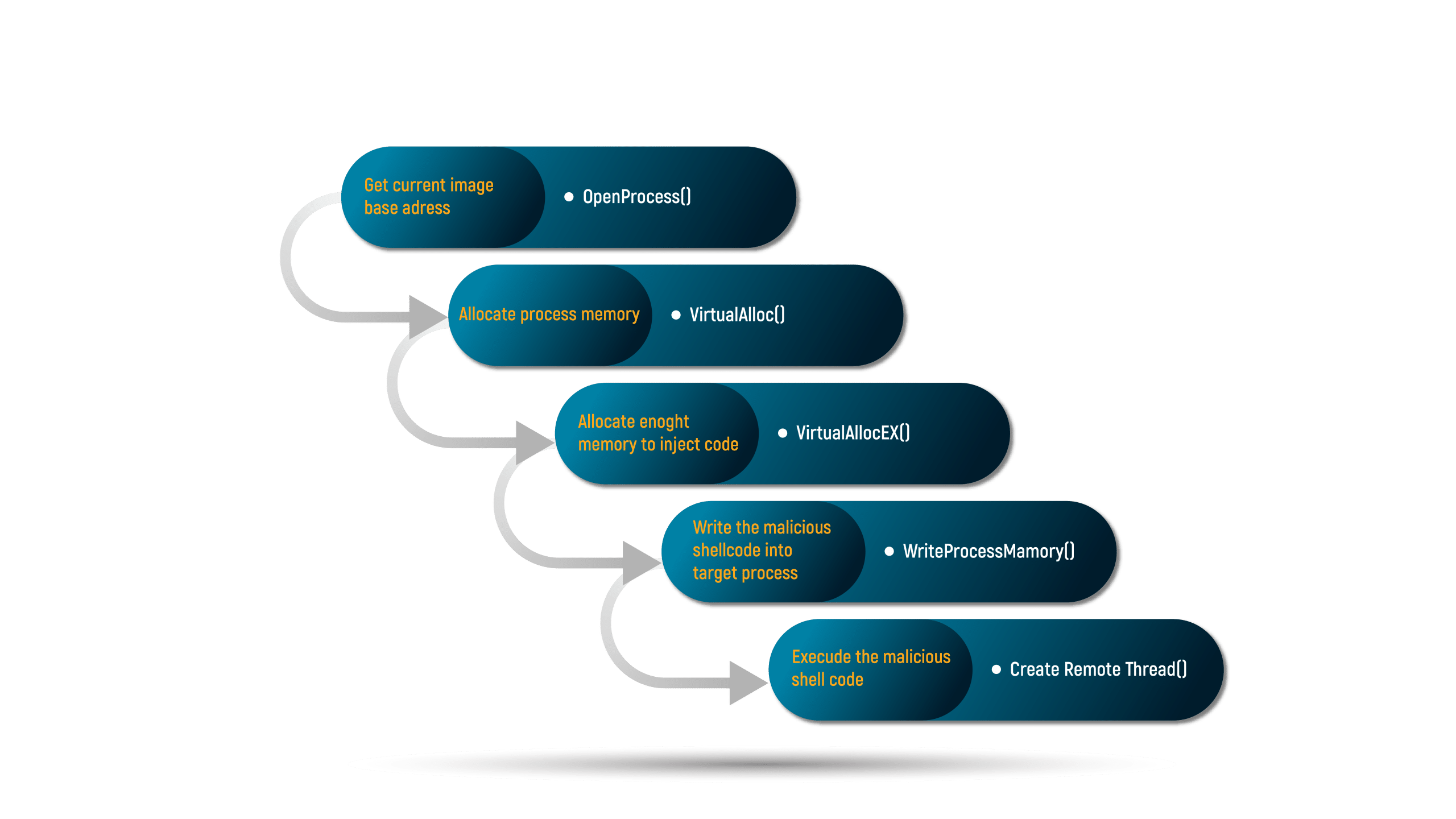
A high-level illustration of memory-safety attacks exploitation strategies. | Download Scientific Diagram

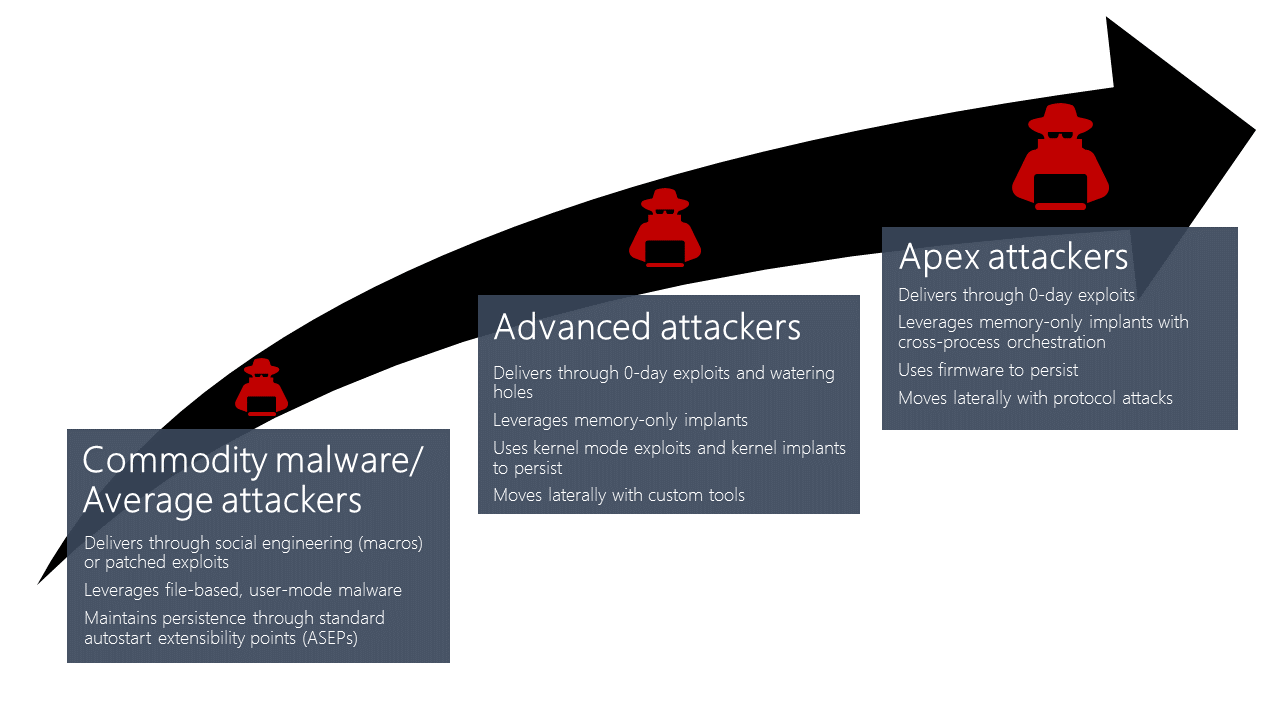
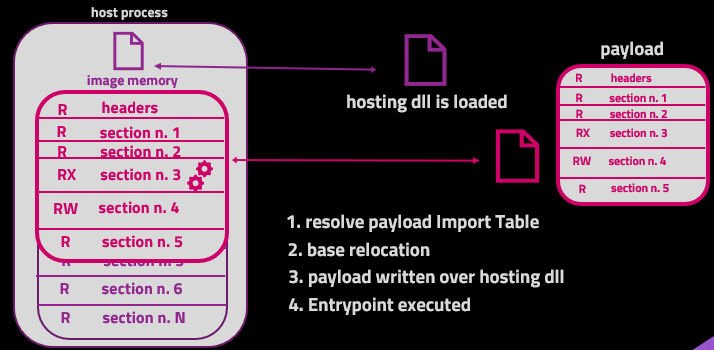
ModuleShifting - Stealthier Variation Of Module Stomping And Module Overloading Injection Techniques That Reduces Memory IoCs
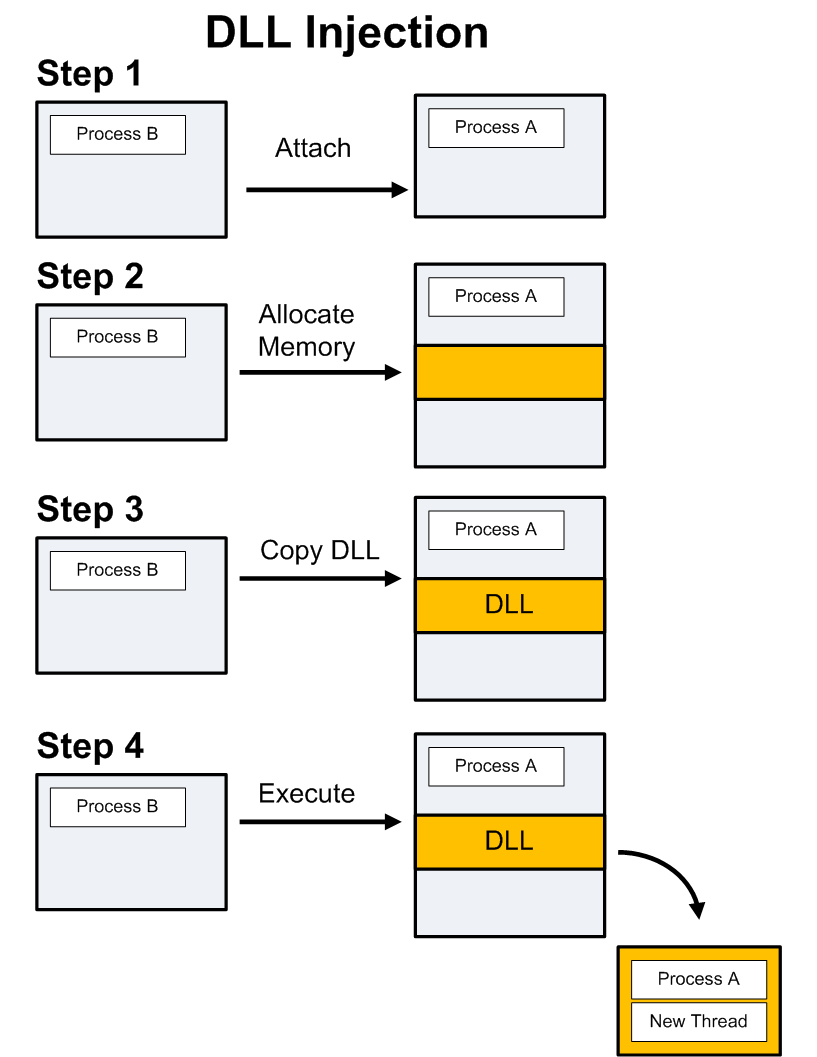
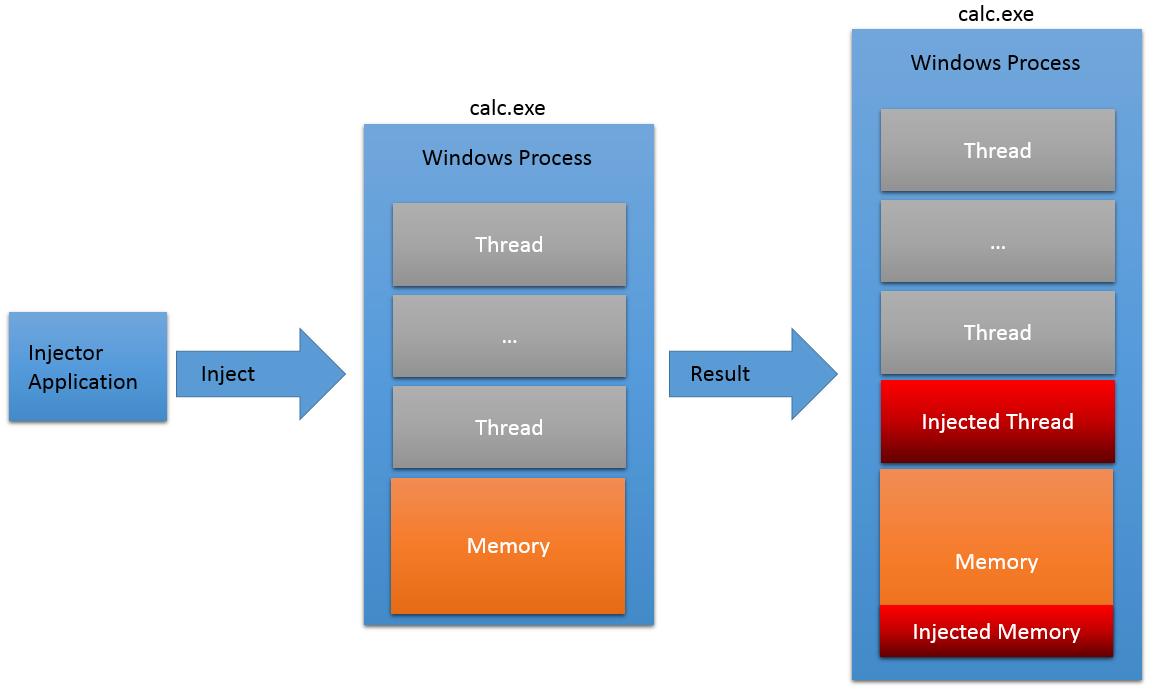
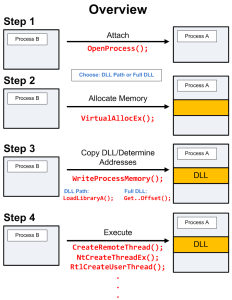
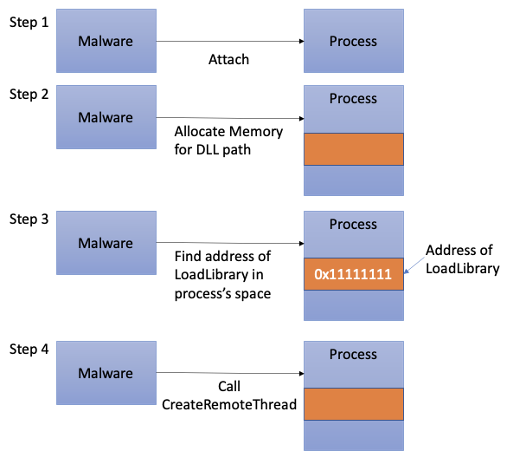
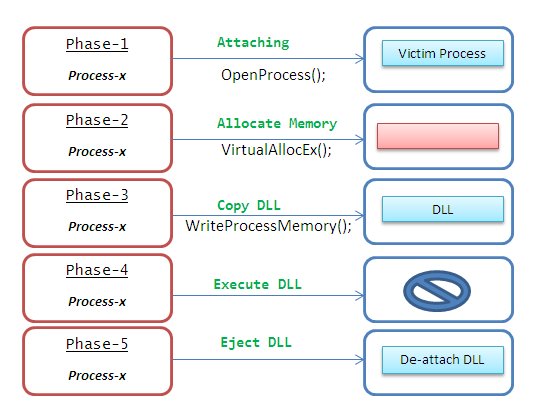
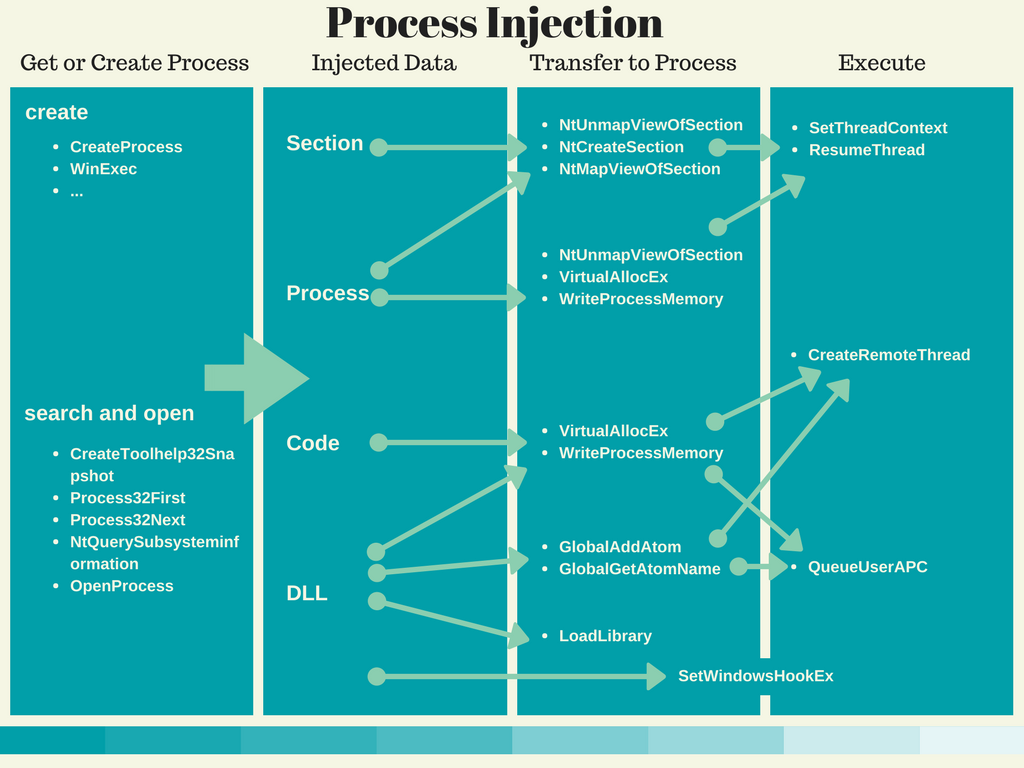
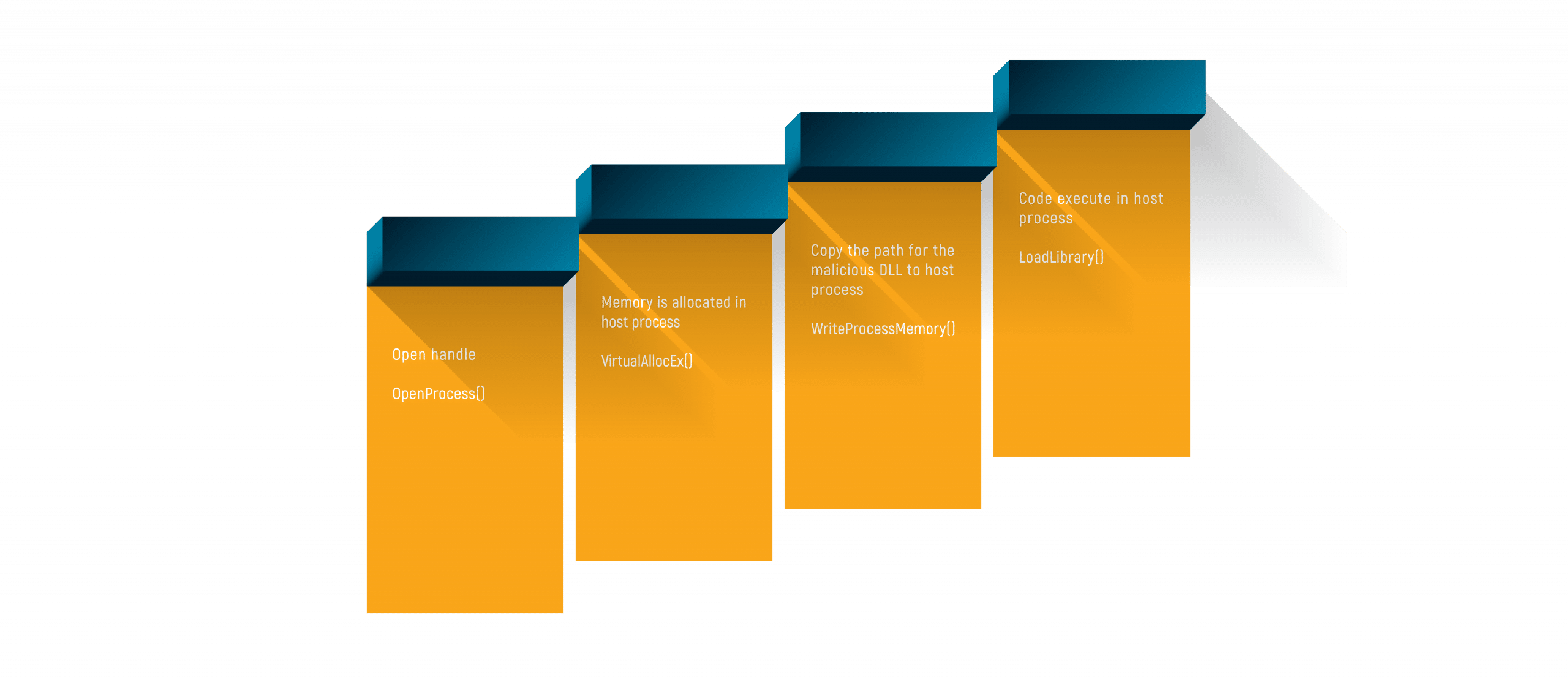
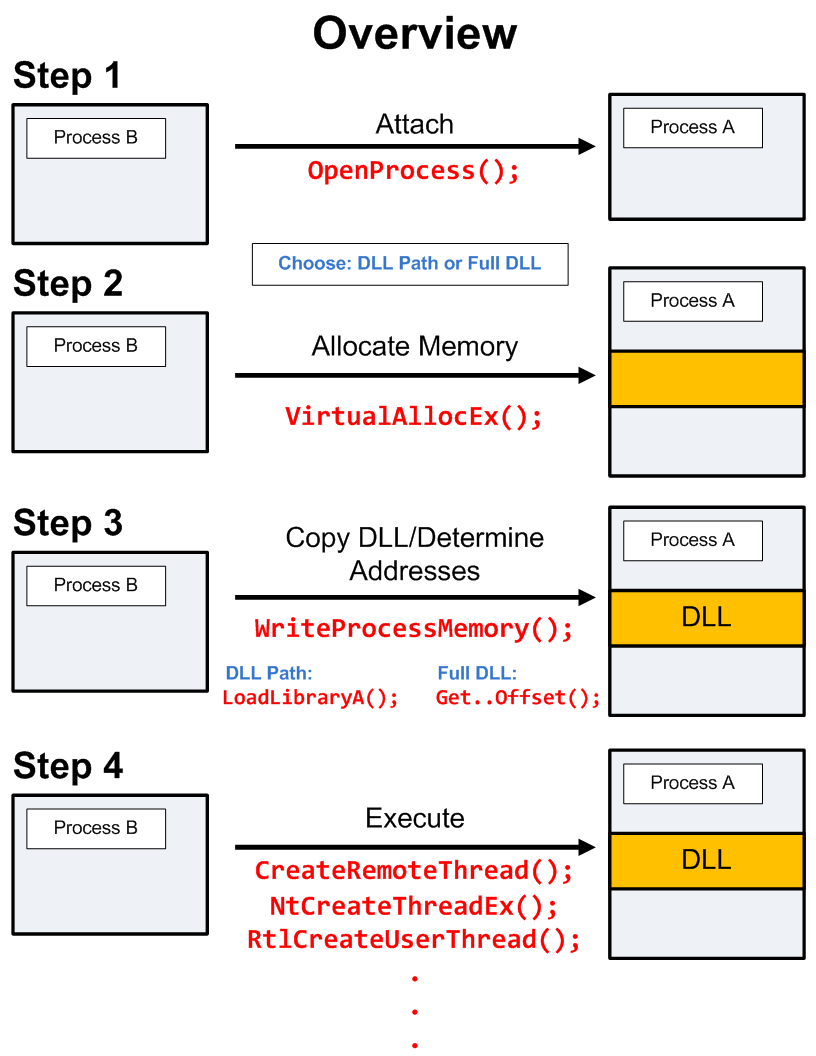
Ten process injection techniques: A technical survey of common and trending process injection techniques | Elastic Blog
Ten process injection techniques: A technical survey of common and trending process injection techniques | Elastic Blog